Here’s the five options I’ve been able to find – so far – if you need fine-grained detail on your Azure subscription usage. (i.e. historically showing user access for security audits across multiple resource groups, etc.)
If you want a one-sentence recommendation – sorry I have to stick with “It depends”. I think you get great power with the OMS option (#2), but the PowerBI option (#3) is up and coming and very robust.
- Option 1: Powershell Client for Azure RM. See the links below for more on this.
- Option 2: Operational Insights
- Option 3: Azure built in portal reporting
- Option 4: PowerBI consuming the REST service. (See the links but this may very well be your best and most powerful option)
-
Option 5: Other tools consuming the ARM auditing APIs/SDK/CLI. There’s lots of log aggregation tool ranging from Excel to very sophisticated third party tooling that consumes the REST interface.
In more detail:
Option #1 – Powershell
This was what we used two years ago. Nowadays, it seems like best practice is log aggregation–using Operations Management Service. That gives you the best level of customization and fine grained detail without having to take on PS scripting or consuming REST endpoints manually.
Auditing reports using ARM Powershell, which in turn rests on the REST API we expose as part of the Azure resource manager. A Microsoft walkthrough of setup including deployment is here.
There’s a good walkthrough on installing Powershell Client for Azure Resource Manager here. This blog goes through this in detail, including answers like ‘who accessed by subscription in the past 60 days”, “what access does a specific user have”, etc. We could extend this to show more detail points.
There’s a walkthu on this blog of building out auditing reports. This blog uses ARM Powershell to come up with user list on subscriptions, modules used etc. And of course there’s third party products offering services in this space as well.
The auditing APIs are evolving fast per my friends on the product team – there are some great third party tools out there that will provide this info. For you script based junkies – PS might be a great option. You can use PowerShell to view the Azure Activity Logs, showing all operations on the subscription and who did what. From here you can consume those API’s – fairly easily – and then you can crunch them into something useful.
Start with the PS Commandlet Get-AzureRmLog:
https://msdn.microsoft.com/en-us/library/mt603617.aspx
https://azure.microsoft.com/en-us/documentation/articles/resource-group-audit/
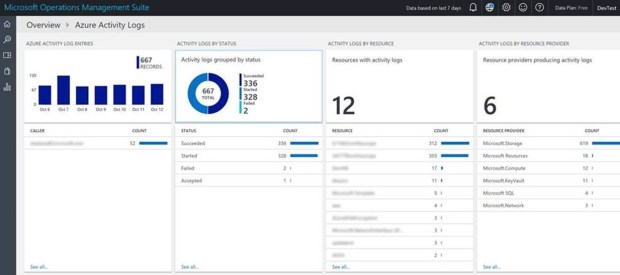
Option 2 – Operational Insights
On #2 above, there’s an overview here of Operational Insights. A overview page on Log Analytics is here, documentation and FAQ is here, Not too much deep dive info on Operational Management Service (OMS) within Premier, but if you think this is a worthwhile option we can engage with a PFE and even build you out a pilot on it. It can also now be connected directly to OMS (as well as Event Hubs and storage accounts). For the type of reporting you are talking about I think OMS would be the answer.
Also worth pointing out that this is only activities carried out though ARM. If you want to see the audit records for changes to RDFE resources i.e. Classic Cloud services etc. then you still need to use the Operation Logs in the classic portal (or API). This caught me out recently trying to help a customer audit config changes to cloud services.
Option #3 – Built in reporting in Azure
Note that the audit data from Azure (ARM) is now available and searchable in the Azure Portal via the Activity Logs blade.

-
According to this article, there’s five different types of reporting available to subscription admins OOTB.
- Anomaly reports – Contain sign in events that we found to be anomalous. Our goal is to make you aware of such activity and enable you to be able to make a determination about whether an event is suspicious.
- Integrated Application reports – Provides insights into how cloud applications are being used in your organization. Azure Active Directory offers integration with thousands of cloud applications.
- Error reports – Indicate errors that may occur when provisioning accounts to external applications.
- User-specific reports – Display device/sign in activity data for a specific user.
- Activity logs – Contain a record of all audited events within the last 24 hours, last 7 days, or last 30 days, as well as group activity changes, and password reset and registration activity.
Option 4 – PowerBI
There’s a couple of slick ways to build out PowerBI reports direct from the REST endpoints. Some great references on this here.

https://azure.microsoft.com/en-us/blog/analyze-azure-audit-logs-in-powerbi-more/ – this goes through the Power BI Content Pack for Azure Audit Logs. There’s a secondary article right here with some snapshots. From this doc:
“In a nutshell, Azure Audit Logs is the go-to place to view all control plane events/logs from all Azure resources. It includes system and user generated events. You can also access this through the Azure Insights SDK, PowerShell, REST API and CLI. The logs are preserved for 90 days in Azure’s Event Logs store.”
Here’s the data you can gather:
- Events by any particular resource over time
- Which users perform what actions, how frequently and on what resources
- Actions and events per subscription, resource group, region etc.
- Azure Service Health (outages and maintenance) events that potentially impacted your resources
- Alerts and AutoScale events by resource and time
- Failures, success of deployments and registrations
Microsoft has further documentation explaining how you can access Azure Audit Logs in the Azure Portal.
Option 5 – Other options:
- There’s advanced reporting available in Azure Active Directory as well. Azure Active Directory Premium. Advanced reports help you improve access security, respond to potential threats and get access to analytics on device access and application usage. There’s a walkthrough of this at this page.
I hope to add to this in the future with some great third party tooling we could recommend. Stay tuned!